On this weblog in regards to the design, deployment and automation of the Black Hat community, we’ve the next sections:
- Designing the Black Hat Community, by Evan Basta
- AP Placement Planning, by Sandro Fasser
- Wi-Fi Air Marshal, by Jérémy Couture, Head of SOC, Paris 2024 Olympic Video games
- Meraki Dashboards, by Rossi Rosario Burgos
- Meraki Programs Supervisor, by Paul Fidler
- A Higher Solution to Design Coaching SSIDs/VLANs, by Paul Fidler
Cisco is honored to be a Premium Accomplice of the Black Hat NOC, and is the Official Community Platform, Cellular System Administration, Malware Evaluation and DNS (Area Title Service) Supplier of Black Hat.

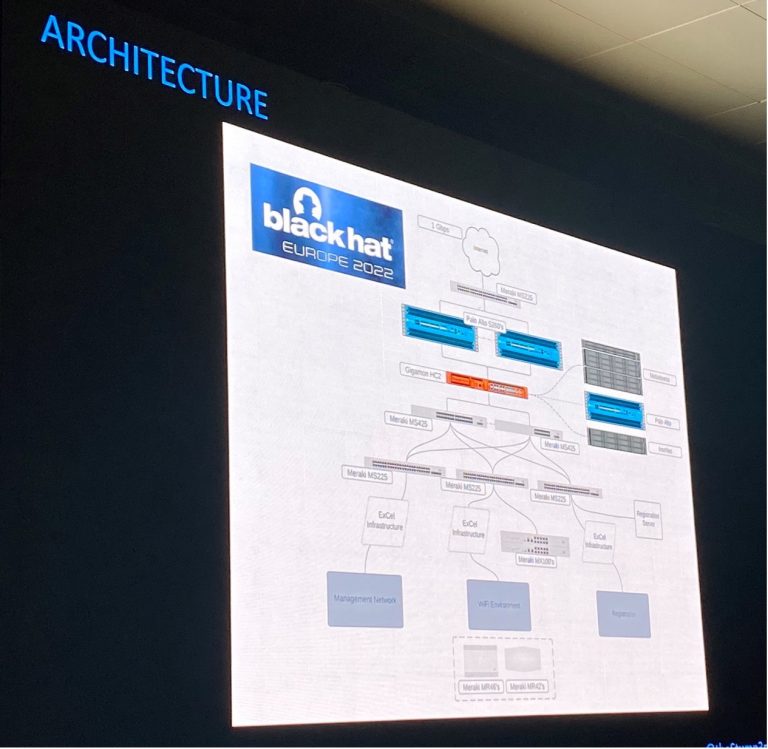
2022 was Cisco’s sixth 12 months as a NOC accomplice for Black Hat Europe. Nevertheless, it was our first time constructing the community for Black Hat Europe. We used experiences of Black Hat Asia 2022 and Black Hat USA 2022 to refine the planning for community topology design and tools. Beneath are our fellow NOC companions offering {hardware}, to construct and safe the community, for our joint buyer: Black Hat.

Designing the Black Hat Community, by Evan Basta
We’re grateful to share that Black Hat Europe 2022 was the smoothest expertise we’ve had within the years at Black Hat. That is due to the 15 Cisco Meraki and Cisco Safe engineers on website (plus just about supporting engineers) to construct, function and safe the community; and nice NOC management and collaborative companions.
To plan, configure, deploy (in two days), keep resilience, and get well (in 4 hours) an enterprise class community, took lots of coordination. We respect the Black Hat NOC management, Informa and the NOC companions; assembly every week to debate the perfect design, staffing, gear choice and deployment, to fulfill the distinctive wants of the convention. Take a look at the “Meraki Unboxed” podcast – Episode 94: Learnings from the Black Hat Europe 2022 Cybersecurity Occasion
We should permit actual malware on the Black Hat community: for coaching, demonstrations, and briefing periods; whereas defending the attendees from assault inside the community from their fellow attendees, and forestall dangerous actors from utilizing the community to assault the Web. It’s a essential steadiness to make sure everybody has a protected expertise, whereas nonetheless with the ability to be taught from actual world malware, vulnerabilities, and malicious web sites.

Along with the weekly conferences with Black Hat and the opposite companions, the Cisco Meraki engineering staff of Sandro Fasser, Rossi Rosario Burgos, Otis Ioannou, Asmae Boutkhil, Jeffry Handal and I met each Friday for 2 months. We additionally mentioned the challenges in a Webex area with different engineers who labored on previous Black Hat occasions.
The mission:
Division of labor is important to scale back errors and keep laser centered on safety scope. Otis took the lead engaged on community topology design with Companions. Asmae dealt with the port assignments for the switches. Rossi ensured each AP and Change was tracked, and the MAC addresses had been supplied to Palo Alto Networks for DCHP assignments. Otis and Rossi spent two days within the server room with the NOC companions, guaranteeing each change was working and configured appropriately. Rossi additionally deployed and configured a distant Registration change for Black Hat.
AP Placement Planning, by Sandro Fasser
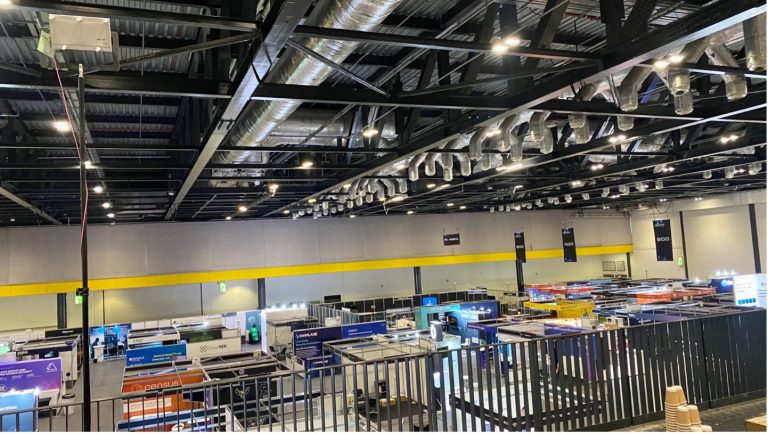
Within the weeks earlier than deployment, our digital Meraki staff member, Aleksandar Dimitrov Vladimirov, and I centered on planning and making a digital Wi-Fi website survey. A number of necessities and restrictions needed to be considered. The report was based mostly on the ExCel centre flooring plans, the area allocation necessities from Black Hat and the variety of APs we had obtainable to us. Though difficult to create, with some uncertainties and sometimes altering necessities as a result of variety of stakeholders concerned, the surveys AP placement for greatest protection ended up being pivotal on the occasion.
Beneath is the Sign Energy plan for the Expo Corridor Ground on the 5 GHz band. The unique plan to go along with a dual-Band deployment was adjusted onsite and the two.4 GHz band was disabled to reinforce efficiency and throughput. This was a choice made through the community setup, in coordination with the NOC Management and based mostly on expertise from previous conferences.

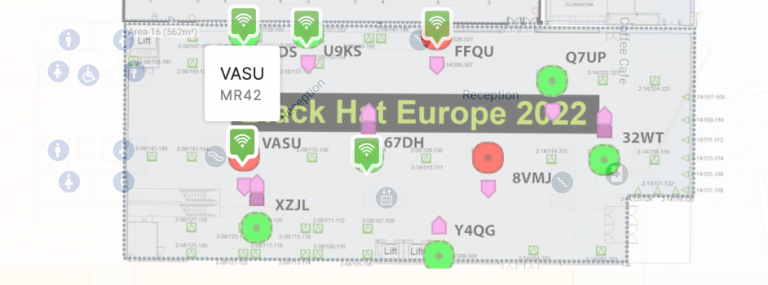
Upon arrival on the ExCel Centre, we carried out a walkthrough of the area that the majority of us had solely seen as a flooring plan and on some pictures. Due to good planning, we may begin deploying the 100+ APs instantly, with solely a small variety of adjustments to optimize the deployment on-site. Because the APs had been pre-staged and added to the Meraki dashboard, together with their location on the ground maps, the primary work was putting and cabling them bodily. Throughout operation, the ground plans within the Meraki Dashboard had been a visible assist to simply spot an issue and navigate the staff on the bottom to the best spot, if one thing needed to be adjusted.
Because the sponsors and attendees crammed every area, within the Meraki dashboard, we had been capable of see in real-time the variety of purchasers related to every AP, presently and over the time of the convention. This enabled fast response if challenges had been recognized, or APs may very well be redeployed to different zones. Beneath is the ExCel Centre Capital Corridor and London Suites, Degree 0. We may change between the 4 ranges with a single click on on the Ground Plans, and drill into any AP, as wanted.
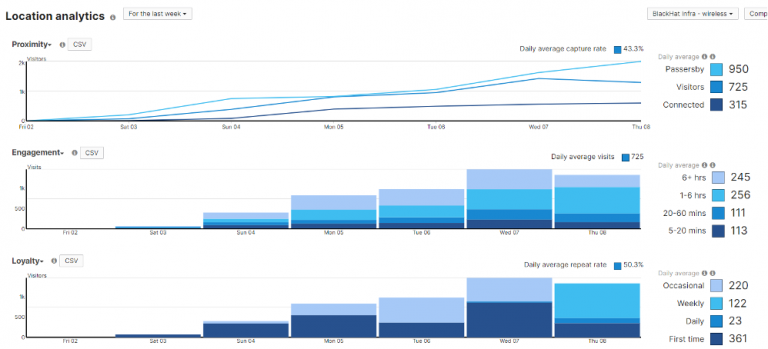
The Location heatmaps additionally supplied important visibility into convention site visitors, each on the community and footfalls of attendees. Bodily safety can be an necessary side of cybersecurity; we have to understand how gadgets transfer in area, know the place invaluable belongings are positioned and monitor their security.
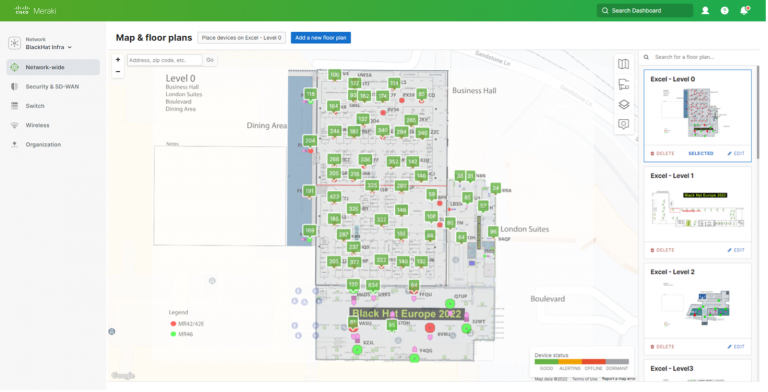
Beneath is the Enterprise Corridor at lunchtime, on the opening day of the convention. You’ll be able to see no reside APs within the backside proper nook of the Location heatmap. That is an instance of adapting the plan to actuality onsite. In previous Black Hat Europe conferences, the Foyer in that space was the primary entrance. Building in 2022 closed this entrance. So, these APs had been reallocated to the Degree 1 Foyer, the place attendees would naturally stream from Registration.
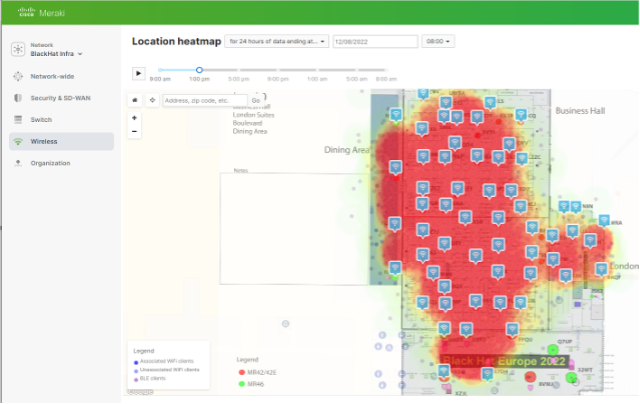
The ground plans and heatmaps additionally helped with the Coaching, Briefings and Keynote community resilience. Capability was simple so as to add briefly, and we had been capable of take away it and relocate it after an area emptied.
Meraki API Integration for computerized machine blocking
Throughout our time within the NOC, we had the prospect to work with different vendor engineers and a few use circumstances that got here up led to attention-grabbing collaborations. One particular use case was that we wished to dam wi-fi purchasers, that present some malicious or dangerous conduct, routinely after they’ve been recognized by one of many SOC analysts on the totally different safety platforms, as well as we wished to indicate them a pleasant warning web page that guides them to the SOC for a pleasant dialog.
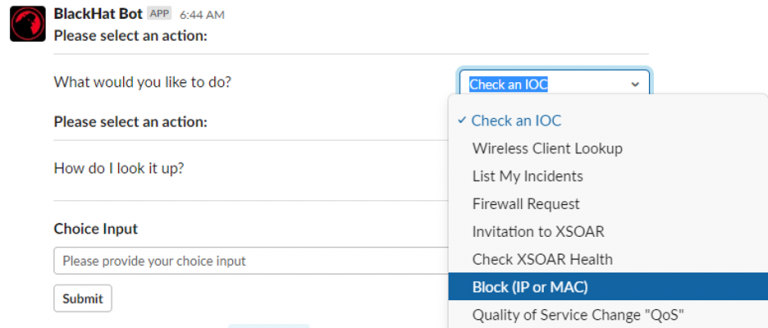
The answer was a script that may be triggered via the interfaces of the opposite safety merchandise and attaches a bunch coverage via the Meraki Dashboard, together with a quarantine VLAN and a splash web page, through the Meraki APIs. This integration was simply one of many many collaboration bits that we labored on.
Wi-Fi Air Marshal, by Jérémy Couture, Head of SOC, Paris 2024 Olympic Video games
Throughout the first day of coaching, within the Meraki dashboard Air Marshal, I noticed packet flood assaults, towards we had been capable of adapt and stay resilient.

I additionally noticed an AP spoofing and broadcast de-authentication assault. I used to be capable of shortly determine the placement of the assault, which was on the Foyer exterior the Enterprise Corridor. Ought to the assaults proceed, bodily safety had the data to intervene. We additionally had the power to trace the MAC tackle all through the venue, as mentioned in Christian Clasen’s part partially two.
![]()
![]()
From our experiences at Black Hat USA 2022, we had encrypted frames enabled, blunting the assault.
Meraki Dashboards, by Rossi Rosario Burgos
The Meraki dashboards made it very simple to watch the well being of the community APs and Switches, with the power to combination information, and shortly pivot into any change, AP or purchasers.

By the phases of the convention, from two days of pre-conference setup, to centered and intense coaching the primary two days, and transition to the briefings and Enterprise Corridor, we had been capable of visualize the community site visitors.
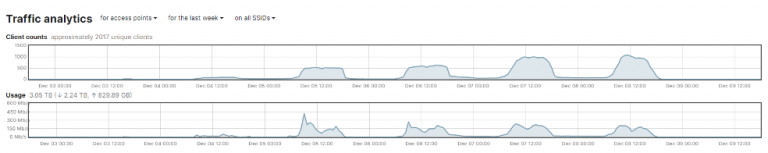
As well as, we may see the variety of attendees who handed by means of the lined space of the convention, with or with out connecting to the community. Christian Clasen takes this obtainable information to a brand new stage in Half 2 of the weblog.
Because the particular person with core tasks for the change configuration and uptime, the Meraki dashboard made it quite simple to shortly change the community topology, based on the wants of the Black Hat buyer.

Meraki Programs Supervisor, by Paul Fidler
Should you refer again to Black Hat USA 2022, you’d have seen that we had over 1,000 iOS gadgets to deploy, with which we had a number of difficulties. For context, the corporate that leases the gadgets to Black Hat doesn’t use a Cellular System Administration (MDM) platform for any of their different exhibits…Black Hat is the one one which does. So, as an alternative of utilizing a mass deployment expertise, like Apple’s Automated System Enrollment, the iOS gadgets are “ready” utilizing Apple Configurator. This contains importing a Wi-Fi profile to the gadgets as a part of that course of. In Las Vegas, this Wi-Fi profile wasn’t set to auto be a part of the Wi-Fi, leading to the necessity to manually change this on 1,000 gadgets. Moreover, 200 gadgets weren’t reset or ready, so we had these to reimage as effectively.

Black Hat Europe 2022 was totally different. We took the teachings from US and coordinated with the contractor to organize the gadgets. Now, in the event you’ve ever used Apple Configurator, there’s a number of steps wanted to organize a tool. Nevertheless, all of those might be actions might be mixed right into a Blueprint:
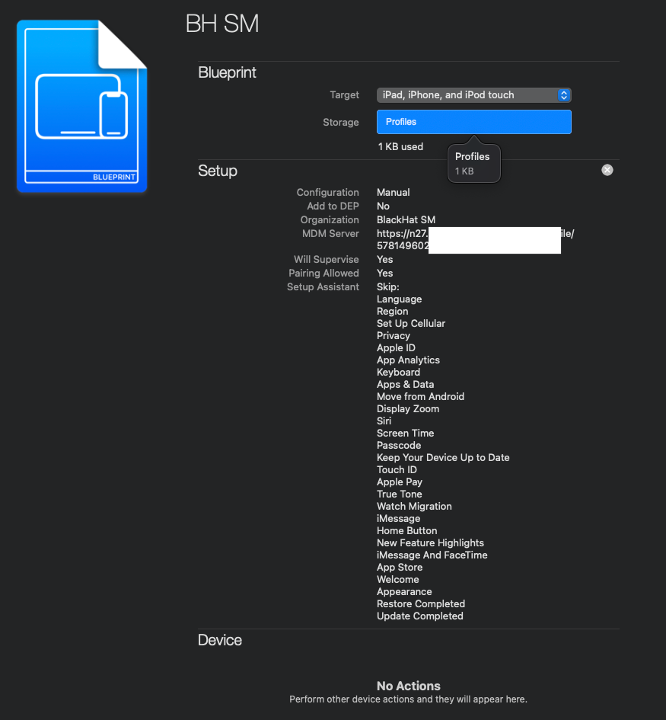
As an alternative of there being a number of steps to organize a tool, there may be now only one! Making use of the Blueprint!
For Black Hat Europe, this included:
- Wi-Fi profile
- Enrollment, together with supervision
- Whether or not to permit USB pairing
- Setup Assistant pane skipping
There’s numerous different issues that may be achieved as effectively, however this ends in the time taken to enroll and arrange a tool to round 30 seconds. Since gadgets might be arrange in parallel (you’re solely restricted by the variety of USB cables / ports you have got), this actually streamlines the enrollment and arrange course of.
Now, for the long run, while you’ll be able to’t Export these blueprints, they’re transportable. Should you open Terminal on a Mac and kind:
cd /Customers/<YOUR USER NAME>/Library/Group Containers/K36BKF7T3D.group.com.apple.configurator/Library/Software Assist/com.apple.configurator/Blueprints
You’ll see a file / package deal referred to as one thing.blueprint This may be zipped up and emailed to some else so, they will then use the very same Blueprint! You could must reboot your laptop for the Blueprint to seem in Apple Configurator.
System Naming / Lock Display Messages
As talked about, the registration / lead seize / session scanning gadgets are supplied by the contractor. Clearly, these are all catalogued and have a singular machine code / QR code on the again of them. Nevertheless, throughout setup, any machine identify provisioned on the machine will get misplaced.
So, there’s three issues we do to know, with out having to resort to utilizing the unwieldy serial quantity, what gadgets is what.
- The very first thing that we do is to make use of the Meraki API to rename Programs Supervisor Gadgets. The script created has another performance too, similar to error dealing with, however it’s attainable to do that with no script. You’ll find it right here. This ensures that the machine has a reputation: iOS gadgets default to being referred to as iPhone or iPad in Programs Supervisor once they first enroll, so, already, that is extremely useful.
- The second factor we do is to make use of a easy Restrictions profile for iOS, which retains the bodily machine’s identify in sync with that within the dashboard
- Lastly, we then use a Lock Display payload to format the message on the machine when it’s locked:

Within the footnote, you’ll see System Title and System Serial in blue. This denotes that the values are literally dynamic and alter per machine. They embody:
- Group identify
- Community identify
- System identify
- System serial
- System mannequin
- System OS model
- System notes
- Proprietor identify
- Proprietor electronic mail
- Proprietor username
- SM machine ID
On the Lock Display, it’s now attainable to see the machine’s identify and serial quantity, with out having to flip the machine over (An issue for the registration gadgets that are locked in a safe case) or open methods preferences.
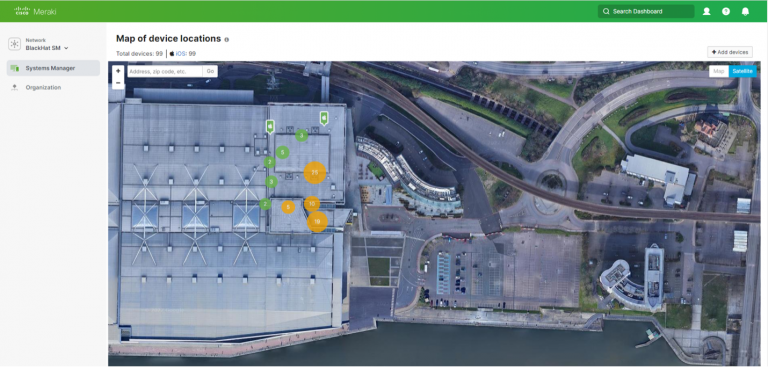
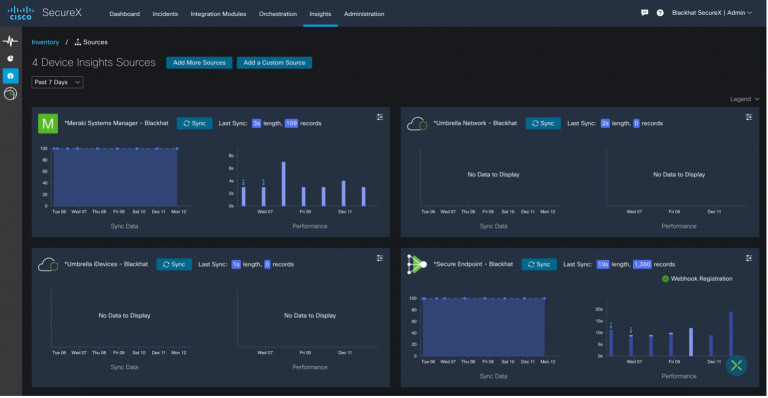
We additionally had integration with SecureX machine insights, to see the safety standing of every iOS machine.
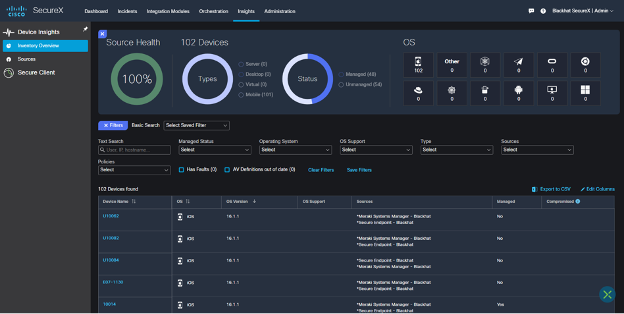
With the power to shortly verify on machine well being from the SecureX dashboard.
Information Safety
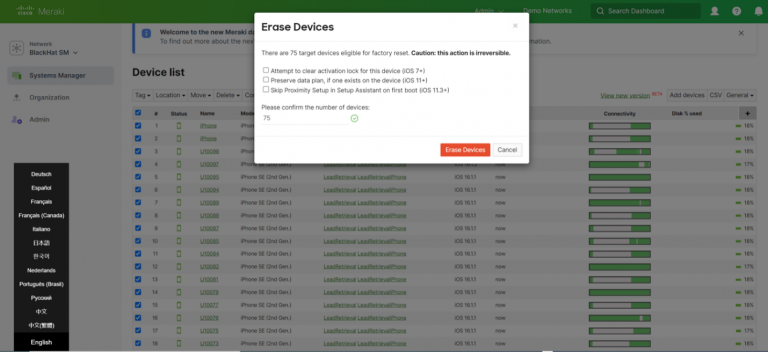
This goes with out saying, however the iOS gadgets (Registration, Lead Seize and Session Scanning) do have entry to private data. To make sure the safety of the info, gadgets are wiped on the finish of the convention. That is extremely satisfying, hitting the Erase Gadgets button in Meraki Programs Supervisor, and watching the 100+ gadgets reset!
A Higher Solution to Design Coaching SSIDs/VLANs, by Paul Fidler
Deploying a community like Black Hat takes lots of work, and repetitive configuration. A lot of this has been lined in earlier blogs. Nevertheless, to make issues simpler for this occasion, as an alternative of the 60 coaching SSIDs we had in Black Hat US 2022, the Meraki staff mentioned the advantages of transferring to iPSKs with Black Hat NOC Management, which accepted the plan.
For context, as an alternative of getting a single pre shared key for an SSID, iPSK performance permits you to have 1000+. Every of those iPSKs might be assigned its personal group coverage / VLAN. So, we created a script:
- That consumed networkID, SSID, Coaching identify, iPSK and VLAN from a CSV
- Created a bunch coverage for that VLAN with the identify of the coaching
- Created an iPSK for the given SSID that referred to the coaching identify
This solely entails 5 API calls:
- For a given community identify, get the community ID
- Get Group Insurance policies
- If the group coverage exists, use that, else create a bunch coverage, retaining the group coverage ID
- Get the SSIDs (to get the ID of the SSID)
- Create an iPSK for the given SSID ID
The majority of the script is error dealing with (The SSID or community doesn’t exist, for instance) and logic!
The end result was one SSID for all of coaching: BHTraining, and every classroom had their very own password. This decreased the coaching SSIDs from over a dozen and helped clear the airwaves.
Acknowledgments
Thanks to the Cisco NOC staff:
- Meraki Community: Evan Basta, Sandro Fasser, Rossi Rosario Burgos, Otis Ioannou, Asmae Boutkhil, Jeffry Handal and Aleksandar Dimitrov Vladimirov
- Meraki Programs Supervisor: Paul Fidler
- Cisco Safe: Ian Redden, Christian Clasen, Aditya Sankar, Ryan MacLennan, Guillaume Buisson, Jerome Schneider, Robert Taylor, Piotr Jarzynka, Tim Wadhwa-Brown and Matthieu Sprunck
- Risk Hunter / Paris 2024 Olympics SOC: Jérémy Couture
Additionally, to our NOC companions NetWitness (particularly David Glover, Iain Davidson, Alessandro Contini and Alessandro Zatti), Palo Alto Networks (particularly James Holland, Matt Ford, Matt Smith and Mathew Chase), Gigamon, IronNet, and the complete Black Hat / Informa Tech employees (particularly Grifter ‘Neil Wyler’, Bart Stump, Steve Fink, James Pope, Jess Stafford and Steve Oldenbourg).

About Black Hat
For 25 years, Black Hat has supplied attendees with the very newest in data safety analysis, improvement, and traits. These high-profile international occasions and trainings are pushed by the wants of the safety neighborhood, striving to deliver collectively the perfect minds within the trade. Black Hat evokes professionals in any respect profession ranges, encouraging development and collaboration amongst academia, world-class researchers, and leaders in the private and non-private sectors. Black Hat Briefings and Trainings are held yearly in the US, Europe and USA. Extra data is obtainable at: blackhat.com. Black Hat is dropped at you by Informa Tech.
We’d love to listen to what you assume. Ask a Query, Remark Beneath, and Keep Related with Cisco Safe on social!
Cisco Safe Social Channels
Share: